
As a Forensics Lab Analyst, you analyse the artefacts from crime scenes. Occasionally, the law enforcement agency you work for receives “intelligence...

As a Forensics Lab Analyst, you analyse the artefacts from crime scenes. Occasionally, the law enforcement agency you work for receives “intelligence...

This blog documents my hands-on investigations using Splunk. I walk through real-world challenges step by step, explaining my thought process, search strategies,...

We will explore the different ways to protect an Ubuntu Server.

This server, SUBCA01, is the “worker bee.” It will stay online, join the domain, and issue certificates to every user and computer...

For my latest home lab project, I am building a Two-Tier Public Key Infrastructure (PKI) to simulate a high-security banking environment.

You’ve definitely run msfvenom, uploaded the payload, and watched it get nuked instantly by Windows Defender. It’s frustrating. It makes you think...

One of the Desktops in the research lab at Organization X is suspected to have been accessed by someone unauthorized. Although they...

In this guide, I’m breaking down how to “live off the land.” We’re talking about taking standard commands and turning them into...
A university’s online registration portal asks students to upload their ID cards for verification. The developer put some filters in place to...

Developers should never trust user input. Even when you think you’ve sanitized everything and even when you’re using the familiar ? placeholder...

This post begins a short series about authentication mistakes I often see in Node.js/Express applications. We’ll look at a real-but-safe example where...

When we accessed the website, we found this:

I made a cool website where you can announce whatever you want! I read about input sanitization, so now I remove any...
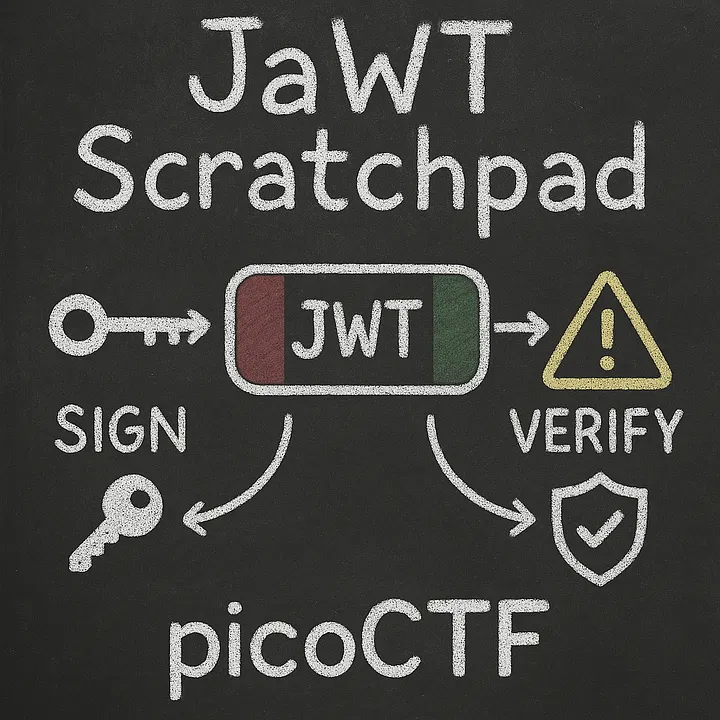
Check the admin scratchpad!
I made a cool website where you can announce whatever you want! Try it out!I heard templating is a cool and modular...

Bookstore ▁▃▅ MEDIUM Objective: understand how a vulnerable API can be exploited Web Exploitation 🔗 Start Challenge →

While searching for jobs on a New York City job portal, I decided to create an account and explore the platform’s features....

Injectics ▁▃▅ MEDIUM Objective: Use your injection skills to take control of a web app. Web Exploitation 🔗 Start Challenge →